The role of open source intelligence in warfare
With the end of the Cold War and the deepening of globalization, the threats facing the country are not only traditional security issues such as military affairs, politics, and diplomacy, but non-traditional security threats such as information-centered cyber warfare. According to estimates by international intelligence experts, 40% to 95% of national intelligence in developed western countries is obtained in the form of open-source intelligence.
In the context of the Russia-Ukraine War, open-source intelligence is very important. Any photo posted on social media may become conclusive evidence of where you are, especially when there are very obvious features in the photo such as a broad background, Iconic buildings, exotic plants, or the position of the sun. As a high-level country, you should pay more attention to hiding your position, otherwise you may attract attacks from enemy countries at any time.
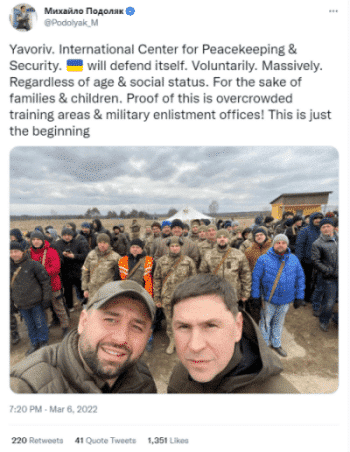
However, high-level Ukrainian government officials did not realize the seriousness of the matter, including President Zelensky, Defense Minister Reznikov, and President’s Office Adviser Podolyak. They post pictures and videos on Twitter every day without any awareness of prevention. The background and buildings behind them are clearly visible. What's even more outrageous is that they will describe where they are located in the text. This is not to mislead the Russian army as everyone imagines, but they really have no security awareness. One of the main ways for the Russian army to obtain Ukrainian intelligence is to read the Twitter of high-level Ukrainian officials every day.
On March 6, 2022, Podolyak tweeted a show-off message, exposing the location of foreign mercenaries. On March 13, 2022, a week after the location was exposed, the International Peacekeeping and Security Center, where Podolyak took pictures, was attacked by 8 Russian missiles, killing 35 people, injuring 134, and destroying many buildings .
When intelligence collection extends to external sources, the likelihood of obtaining intelligence becomes greater. Make full use of open source intelligence collection systems such as Knowlesys Intelligence System to locate and collect sensitive information before taking action, so that more useful data can be mined.
【Dark Web】●5 Awesome Dark Web Links
銆怬pen Source Intelligence銆戔棌5 Hacking Forums Accessible by Web Browsers
銆怤etwork Security銆戔棌9 popular malicious Chrome extensions
銆怤ews銆戔棌Access control giant hit by ransom attack, NATO, Alibaba, Thales and others affected
【Open Source Intelligence】●10 core professional competencies for intelligence analysts
【Artificial Intelligence】●Advanced tips for using ChatGPT-4
【News】●AI-generated fake image of Pentagon explosion goes viral on Twitter



