New ransomware group has compromised multiple organizations in US, South Korea
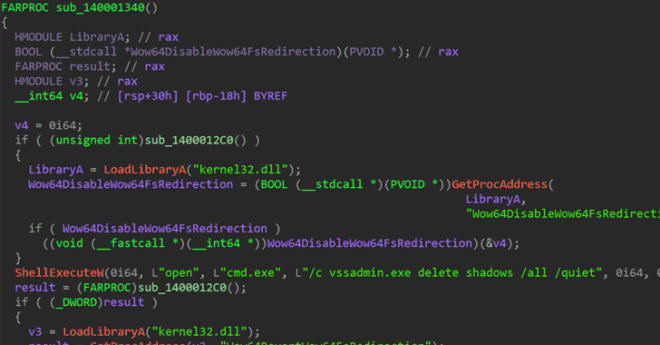
A new ransomware group called RA Group has recently come into the spotlight, a cybercriminal group that has been "on the move" since April 22, 2023, and is still rapidly expanding its ransom campaign.
In a report shared with the Hacker News, security researcher Chetan Raghuprasad noted that RA Group has so far compromised three organizations in the United States and one in South Korea across multiple verticals, including manufacturing, wealth management, insurance providers and pharmaceuticals.
RA Group operates an information breach website where they conduct double ransom attacks on victims to force them to pay ransom.
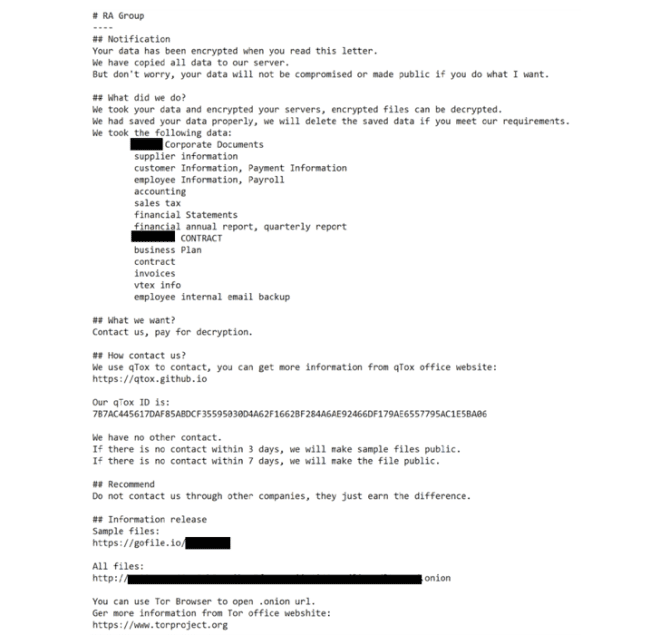
Raghuprasad explained that RA Group uses customized ransom notes, which include the victim's name and a unique link to download the leaked evidence. If the victim does not contact the group within three days, then they will simply leak the victim's information.
In addition, the group takes steps to avoid encrypting system files and folders through hard-coded lists, which allow victims to download the qTox chat application. Victims can contact the group via the qTox ID provided on the ransom note.
RA Group differs from other ransomware in that they host the information on a secure TOR site and then sell the victims' compromised data directly on their leaked website.
About a week ago, SentinelOne said that there are now a number of threat actors who have developed more than a dozen variants capable of targeting Linux systems through the Babuk ransomware code. At the same time, more and more hackers are using Babuk builders to develop ESXi and Linux ransomware, which has become a clear trend.
Other ransomware players that have used Babuk source code in the past year include AstraLocker and Nokoyawa. Cheerscrypt is another Babuk-based ransomware. In addition, there are two other new ransomware codenamed Rancoz and BlackSuit, the latter specifically targeting Windows and VMware ESXi servers.
Cyble said these constantly updated ransomware reveals that the current threat actors are a group of people with advanced expertise and agility, who are familiar with the cybersecurity measures currently implemented in various countries and are able to stand against these policies and customize their ransomware.
【Web Intelligence Monitoring】●Advantages of open source intelligence
銆怬pen Source Intelligence銆戔棌5 Hacking Forums Accessible by Web Browsers
銆怤ews銆戔棌Access control giant hit by ransom attack, NATO, Alibaba, Thales and others affected
銆怰esources銆戔棌The Achilles heel of AI startups: no shortage of money, but a lack of training data
【Artificial Intelligence】●Advanced tips for using ChatGPT-4
【Open Source Intelligence】●10 core professional competencies for intelligence analysts
銆怰esources銆戔棌The 27 most popular AI Tools in 2023



