Behavioral Pattern Analysis Through Social Media OSINT
In today's rapidly evolving digital landscape, social media platforms serve as vast repositories of human behavior, interactions, and intentions. Open Source Intelligence (OSINT) practitioners, particularly in law enforcement, national security, and intelligence agencies, increasingly rely on behavioral pattern analysis to uncover hidden threats, map coordinated activities, and predict potential risks. By examining posting frequency, interaction networks, linguistic styles, temporal patterns, and content themes across platforms, analysts can transform scattered public data into actionable insights. Knowlesys Open Source Intelligent System stands at the forefront of this capability, delivering an integrated platform that empowers professionals to conduct comprehensive behavioral analysis with precision and speed.
The Strategic Importance of Behavioral Pattern Analysis in OSINT
Behavioral pattern analysis goes beyond surface-level monitoring; it seeks to understand the "why" and "how" behind online actions. In threat detection scenarios, anomalies such as sudden spikes in activity, synchronized posting across multiple accounts, or shifts in sentiment can signal coordinated campaigns, disinformation efforts, or emerging radicalization. Traditional monitoring often misses these subtle signals, but advanced OSINT tools enable the identification of recurring patterns that reveal organizational structures, operational intents, and individual motivations.
For homeland security and counterterrorism operations, this analysis is indispensable. Coordinated actors frequently exhibit predictable behavioral markers — high-frequency bursts, templated content, and cross-platform amplification — that distinguish them from organic users. Knowlesys Open Source Intelligent System addresses these challenges through AI-driven detection, allowing analysts to construct detailed behavioral profiles and trace linkages across global social networks.
Core Components of Behavioral Analysis on Social Media
Effective behavioral pattern analysis in OSINT draws from multiple dimensions of social media data:
- Activity Patterns: Posting frequency, timing, and diurnal cycles often reveal timezone masking or automated behavior.
- Interaction Networks: Likes, shares, replies, and mentions help map influence clusters and collaborative structures.
- Content Characteristics: Sentiment trends, keyword usage, linguistic consistency, and media types indicate coordinated narratives or individual evolution.
- Metadata Insights: Timestamps, device fingerprints, geolocation tags, and historical changes provide context for anomaly detection.
Knowlesys Open Source Intelligent System excels in integrating these elements, supporting real-time discovery across major platforms while automatically identifying sensitive content in text, images, and videos. Its AI models achieve high accuracy in recognizing behavioral anomalies, reducing manual effort and enhancing investigative efficiency.
Advanced Techniques Employed in Behavioral Pattern Analysis
Modern OSINT leverages machine learning for clustering similar behaviors, anomaly detection for flagging irregularities, and graph-based modeling for visualizing relationships. For instance, analysts can track target accounts over time, evaluate influence through engagement metrics, and trace propagation paths to identify key amplifiers.
Knowlesys incorporates sophisticated features such as fake account identification based on behavioral traits, KOL influence assessment, and event propagation visualization. These capabilities enable the detection of synchronized activities that might indicate orchestrated influence operations or threat actor networks.
The following table illustrates common behavioral indicators and their intelligence value:
| Behavioral Indicator | Description | Intelligence Insight |
|---|---|---|
| High-frequency bursts | Multiple posts in short timeframes | Potential bot or coordinated activity |
| Timezone inconsistencies | Activity patterns not matching claimed location | Possible masking or foreign origin |
| Synchronized content | Similar phrasing across accounts | Evidence of coordinated campaigns |
| Rapid sentiment shifts | Sudden changes in tone or topic | Emerging radicalization or manipulation |
Visualizing Behavioral Patterns for Deeper Insights
Visualization plays a crucial role in understanding complex behavioral networks. Knowledge graphs and heatmaps reveal clusters of activity, propagation flows, and anomaly hotspots.
Here are examples of social network graphs commonly used in OSINT behavioral analysis:
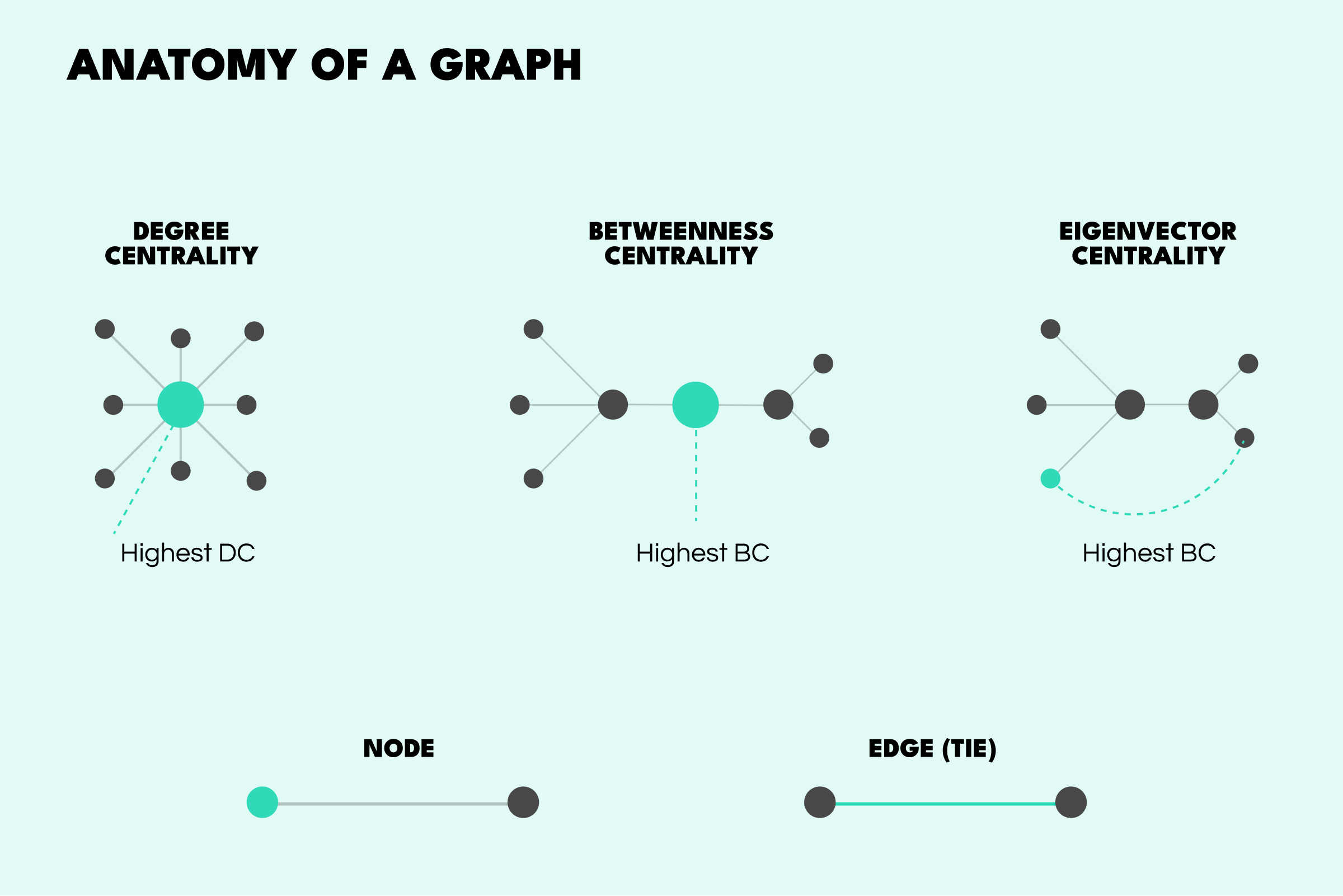

These visual tools help analysts quickly identify central nodes, bridging entities, and unusual clusters that warrant further investigation.
Real-World Applications and Threat Detection
In practice, behavioral pattern analysis supports diverse use cases. Intelligence teams monitor for signs of radicalization through gradual shifts in content and associations. Cybersecurity professionals detect disinformation by tracing synchronized narratives. Law enforcement agencies uncover criminal networks via repeated interactions and shared behavioral markers.
Knowlesys Open Source Intelligent System streamlines these workflows with minute-level early warnings, multi-dimensional analysis, and collaborative features. Its ability to process millions of messages daily, combined with precise AI judgment, ensures timely detection of emerging threats before they escalate.
Conclusion: Elevating Intelligence Through Behavioral Understanding
Behavioral pattern analysis represents a paradigm shift in social media OSINT — moving from reactive monitoring to proactive intelligence. By uncovering the underlying rhythms of online activity, organizations can anticipate threats, disrupt malicious operations, and make evidence-based decisions. Knowlesys Open Source Intelligent System provides the technological foundation for this transformation, offering law enforcement and intelligence professionals a robust, AI-powered platform for intelligence discovery, alerting, analysis, and collaborative workflows. In an era where digital behavior increasingly shapes real-world outcomes, mastering these patterns is essential for maintaining security and strategic advantage.
